Security for Mobile Devices Research Paper Essay.
Journal of Information Security and Applications (JISA) focuses on the original research and practice-driven applications with relevance to information security and applications.JISA provides a common linkage between a vibrant scientific and research community and industry professionals by offering a clear view on modern problems and challenges in information security, as well as identifying.
True Mobile Security solutions continuously detect and protect against cyber attacks around the clock. Download cutting edge Mobile Security White Papers.
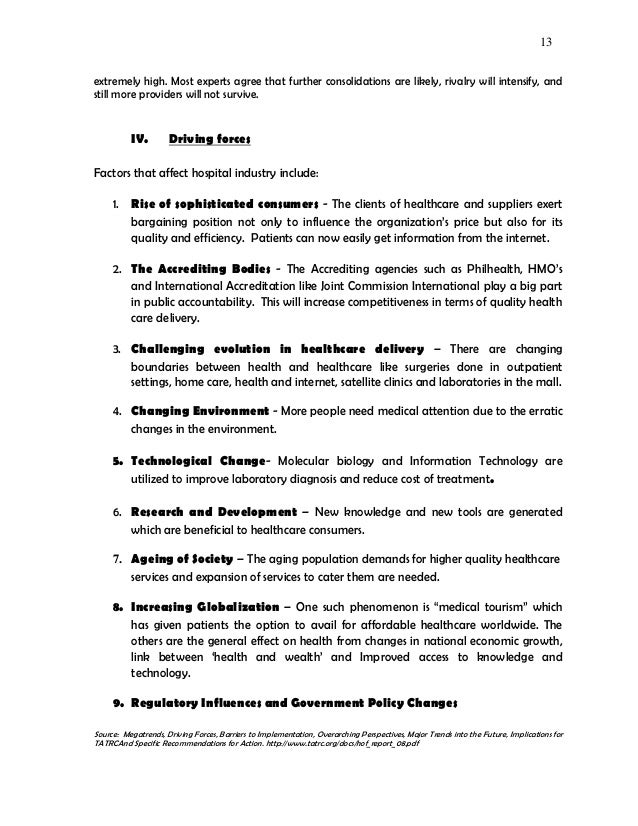
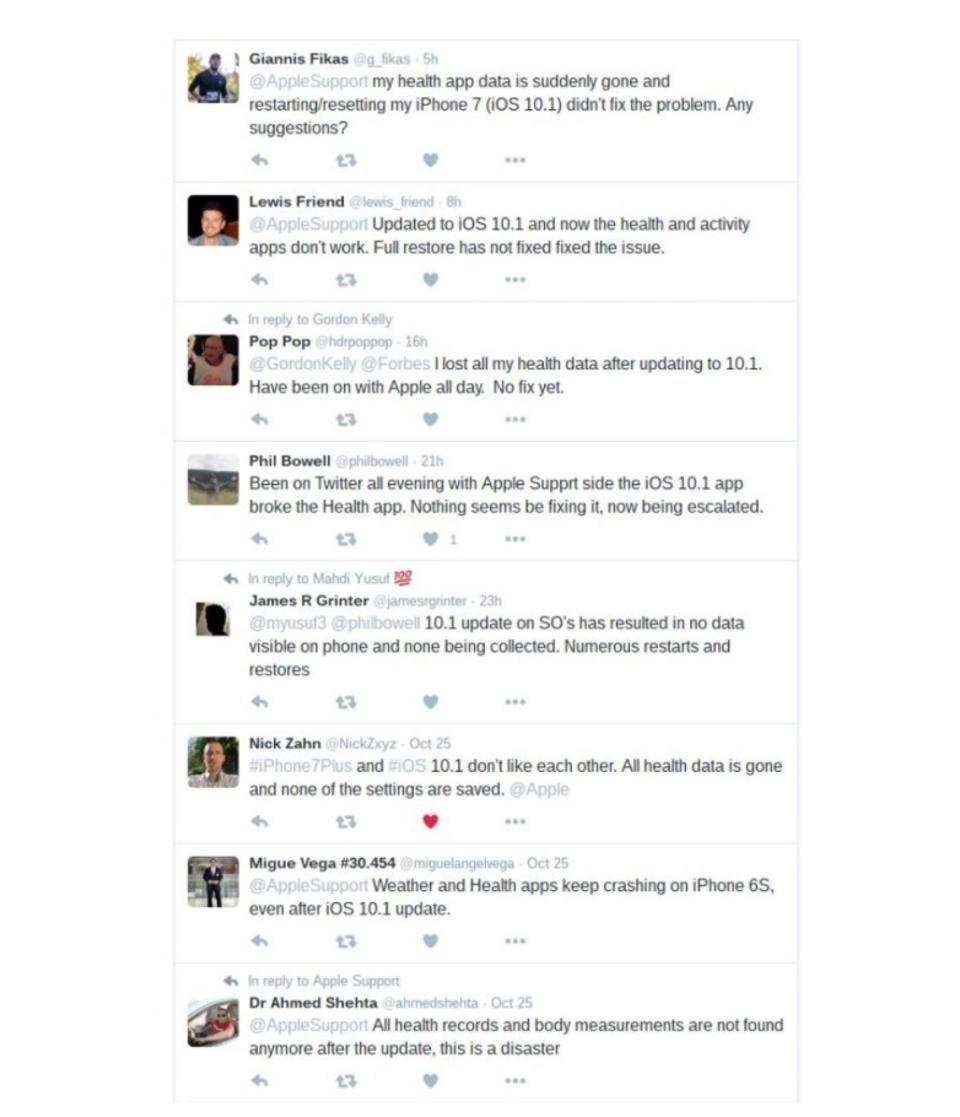
Mobile device security Threats: Over the past two decades, we have witnessed significant technology advances in mobile devices, from the personal data assistants (PDAs) of the late 1990s and early 2000s to the ubiquitous and multifunctional smartphones of today.These advances have extended the virtual boundaries of the enterprise, blurring the lines between home and office and coworker and.
Network security research paper mobile devices Research essay papers marketing corporate governance dissertation green paper procedure for writing a research proposal chemistry networking research papers quantum mechanics. Timetable for research proposals chemistry Review of literatures myanmar volume 2 aim of research paper critical thinking.
Dissertation topics on data security and privacy Over the past decade, there has been a major increase in the volume of data stored or transfered between systems, users, or organisations. Additionally, the rate of sharing personal and corporate data across networks and public cloud platforms has increased greatly.
Research from Essay: Mobile Device Reliability. Factors and Implementation of Mobile Device Security. Mobile devices have become all-pervasive and its use is only growing from here. With such an considerable usage of mobile devices for personal and business employ, its secureness becomes a crucial question. Most devices furore not have the.
N1 - This is the final draft version of the paper that appeared in the journal 'Information Technology', 48, 2006. This article is also available in German. PY - 2006. Y1 - 2006. N2 - Some of the most significant security issues arising in the context of ubiquitous mobile computing are reviewed. Emerging technologies which may be able to help.